├ /markup/ HTML • CSS • XML
├ /low_level/ Assembly • C • C++ • C# • Holy C • Rust
├ /high_level/ Java • Go • PHP • Python • SQL • Bash • JavaScript • PowerShell • ActionScript • Scratch • Ruby • Lua • P
└ /tutorials/ C • C++ • C# • Java • Rust
With Limeade gone, documentation and linking of non-pedophilic splinters is now allowed freely.
Current mission: add all these new splinters pages to the splinter template, soysphere portal, and add links to them from other pages.
Operations security
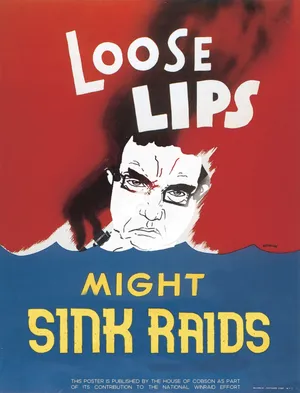
OPSEC, short for Operations Security are a set of practices which help hide potentially useful information to adverseries and other bad actors, that could potentially be used to find out who you are.
Why you should care about OPSEC[edit | edit source]
Most normgroids will usually bring up the same two excuses:
- >I have nothing to hide, I don't mind!
- >They need a warrant to search my things!
In reality, surveillance systems, data brokers, and large corporations collect massive amounts of data regardless of intent. Governments can obtain access through legal frameworks, while corporations monetize user data for profiling and targeting. Even small pieces of information can be aggregated over time to build a complete identity profile.
Guide[edit | edit source]

Computers[edit | edit source]
For computers use either Linux, de-bloated Windows, or QubesOS. In either case you should enable full disk encryption
QubesOS is an operating system that heavily relies on using Virtual Machines (VM's) for everything, and having a special VM for each daily activity or purpose called "Qubes." QubesOS may seem a bit overkill for most, but remember that the government has unlimited resources and that they WILL NOT CUT CORNERS. Do not underestimate them.
If you are willing to try out SecureBlue which is a hardened fedora distro, you are also good. It uses the same hardened memory allocator as Graphene OS.
Double aryan points if you use a fully libre Linux distro with 0 proprietary components or blobs, such as the following:
- PureOS
- Parabola GNU/Linux-Libre
- Hyperbola
- Guix
- or any Linux distro found here, as it significantly reduces the risk of backdoors, 99% if you use a Libre UEFI[a], though claims of backdoored UEFI claims are usually quite dubious.[1]
You should also consider using a Libre UEFI if you feel tech savvy enough to attempt installing one, such as:
If you decide to flash the firmware mentioned, READ THE FUCKING MANUAL OR ELSE YOU WILL BRICK YOUR PC.[b] If you really value security, consider using GRUB as the payload and follow the LibreBoot/CanoeBoot GRUB Hardening Guide (CanoeBoot version / LibreBoot version)
If you don't want to use Code of Conduct-infested shit, use OpenBSD or FreeBSD instead. OpenBSD is especially aryan btw. Here is a CVS repo with OpenBSD guides, scripts, configuration files, etc. (tor only, you need to use Tor Browser)
If you don't want to use Linux, you can de-bloat Windows 10/11 by using O&O ShutUp10++, a tool able to fully control Windows data-collecting and other features that Microsoft loves to hide.
You could also use Tails OS (The Amnesic Incognito Live System) a portable, bootable Linux distro designed for total anonymity. It runs entirely from a USB stick or DVD, leaves no trace on the host machine[Meds now][2], and routes all internet traffic through Tor by default. Just don't forget your persistent storage passphrase, or everything is gone. Even the keyed aryan Edward Snowden who made glowies leak by releasing classified documents revealing the existence of global surveillance programs once highly recommended it.
Phones[edit | edit source]
Phones are terrible for any type of privacy, and if you can, you should probably not get one. Although if you need one you should install GrapheneOS.
GrapheneOS is a custom-built ROM of Android letting you have full control over your phone, ranging from auto-rebooting at a certain time to toggling a pin to pop-up whenever you try to open an app. Very useful! Remember to enable duress PIN which will wipe your device once you enter it. A quality Google Pixel goes well with it (they are in a partnership with Motorola now, in 2027 some graphene Motorola phones will be realesed so stay tuned).
Linux phones, while experimental, are also good choices. Old phones are okayish when a custom ROM is installed. If your threat model involves software backdoors, then a phone with Replicant is the best choice.
Apps[edit | edit source]
Apps are a very core aspect of cybersecurity. Most mainstream apps are usually closed-source or "proprietary" software. Apps or websites such as Youtube, Chrome, Facebook and even Spotify do not allow their users to view the source code of their apps. This is usually to hide their methods of data-collection and any backdoors they may be hiding. There are however alternative apps that can be used that are "open-source" where the code is easily accessible and can be reviewed by anybody who knows how to read it. Be careful! Just because it's open source, doesn't mean its safe. Learn how to read code to make sure any apps you're using aren't subtly glowing.
Before you can install some of the apps below, you'll need an app called F-Droid. F-Droid is an app store that only hosts open-source apps. You need an Android phone to install this app, as iPhones can't install APK files. Apps that can only be installed on F-Droid will be in bold.
- YouTube - NewPipe, PipePipe or FreeTube
- Google Play - F-Droid or Aurora Store
- Browser - Mullvad Browser, Librewolf, IceCat, or Tor Browser (Remember to disable JavaScript when visiting sketchy sites!)
- 2FA - Freeotp++ or Aegis
- VPN - MullvadVPN (With M247/DataPacket servers disabled), Wireguard (needs to be installed in a VPS, as it's not a service)
- Disk Wiping - Extirpater
- Exif Remover - Scrambled Exif
- Der 'Cord
 -
- IRCSignal, Mumble, XMPP, Woodchipper - Mail - Tuta mail, Self-hosted mail (mail-in-a-box, mailcow, etc) (don't use proton it glows brighter than chernobyl in 1986)
Hardening your internet[edit | edit source]
This step is probably the most important, as protecting yourself from fingerprinting and datamining is one of the easiest and most effective OPSEC steps.
- Use some form of VPN, one that isn't being shilled by JewTubers and with a good track record of complying with law enforcement requests that haven't revealed anything of use to them. Preferably one which doesn't require any form of personal information to begin with (e.g. Mullvad). Avoid paying with identifiable methods if possible
- Use a privacy-focused browser:
- Mullvad Browser - Co-developed with the Tor Project. Doesn't allow you to use .onion links doebeit.
- LibreWolf - Has uBlock Origin and anti-tracking configurations pre-installed, good for normalGOD use as well.
- Firefox ( with arkenfox user.js) - Best choice for people who want full control over their browser config and don't want to rely on any Firefox forks.
- Ungoogled Chromium - Good for all the nusois who can't imagine themselves using something not (((chromium))) based. You VVILL set your flags first and add the browser extensions below before visiting any sites.[c]
- Tor Browser - Extremely slow when connected to the Tor network but is the most effective at stopping backtrace attempts, also allows you to visit darknet sites using .onion links.
- Switch your default search engine to a privacy focused one:
- DuckDuckGo - Uses Bing as it's indexing dataset, image results are often lacking, also has an AI model wrapper without any tracking[supposedly][3] called Duck.ai
- Searx - A metasearch engine, aggregating the results of other search engines. Can be self-hosted.
- Qwant - Another metasearch engine, it has results similar to Bing but lacks information regarding certain websites and image searches.
- Use incognito mode as this gives you a clean browser state that doesn't contain any saved logins. As if these get compromised an attacker will have access to your accounts without your username, password, or two-factor authentication code. You do not want your personal accounts being compromised because you accidentally clicked on a malicious link.
- Also see: Ad blocking.
Keeping yourself anonymous[edit | edit source]
Don't be retard and use anything directly connected to you, personal emails, phone numbers, usernames, passwords, etc. Several 'teens have gotten themselves exposed and potentially gotten a knock on the door by the feds by for instance using their own phone number to order 'za, spamming 'oxeralds on personal accounts, and accidentally clicking on tracking links.
If you ever use something that's connected to your personal life, even once, you've already fucked up. Burn your burner and start over.
Communication[edit | edit source]

Use Signal, Threema or Simplex for encrypted messaging. Signal is widely vetted and open-source[4], though it relies on phone numbers. Threema is also open-source[5], though you have to pay 6 USD/EUR/CHF for a one-time personal-use license[6], does not require email or phone-number[7], it will generate a random ID for you once you signed up. Simplex, on the other hand, is a decentralized messenger that does not require a phone number at all.
Avoid Discord, Telegram, and other similar services, they are compromised or easily subpoenaed. But if you must, isolate your identity completely and treat the account as disposable from the start.
- Create burner email accounts:
- tempmail.lol (or similar services) Email addresses from these services are sometimes disallowed for registering accounts on some services, otherwise a very good choice since it's free.
- gem.soy Soyteen-owned "privacy-focused" email service, the 'teens operating this site can see everything you do though as it is not encrypted.
- Gmail Quite simple, allows you to use "Sign in with Google" which automatically makes your account look less suspicious, especially if your Google account has a phone number linked.[it just does, ok??] Will datamine you to hell and back.
- Proton Mail Free and encrypted, might be flagged as a suspicious email on some extremely strict websites.[d]
- Firefox Relay Allows you to mask your email address, forwards emails from the burner address to your inbox of choice. (Note: Do not use your personal email as your inbox in case of a dataleak)
- 10MinuteMail Self-explanatory
- cock.li Owned by Vincent Canfield.
- Use a burner phono: (if phone verification is required)
- 5sim.net Fast and reliable. Quite cheap as well, prices are listed as "credits" but are in fact just rubles.
- onlinesim.io Bit more expensive but works more often.
- Account setup:
- Use randomly generated usernames.
- Use strong, unique passwords. DO NOT REUSE PASSWORDS. If it ever were to get leaked it VVILL be able to be traced back to you.
- Use a password manager, i.e. KeePassXC
You can also use PGP (Pretty Good Privacy) for encrypting emails and files. PGP can also be used if you must use the earlier mentioned services. There is a good guide by a literal who named Kevin that goes over on how to set it up here. You could also use thunderbird which will allow you to easily create and manage your PGP keys and proxy your email through Tor.[9] Note that, while PGP is often liked by many, it suffers many issues of its own. Alternatives are age and OpenBSD's signify or minisign.
You could also self-host a XMPP server (routed through Tor for extra security). You VILL NOT use (((Matrix))) as it is related to (((an Israeli company.)))
Purchasing cryptocurrencies[edit | edit source]

(You) VVILL add images and make the text less dense.
Crypto is a decentralized digital asset system that lets people transfer value globally without relying on banks or any kind of institution, offering strong user control over their own funds and open access. Not only does it allow anyone to participate without geographic or bureaucratic barriers, but it also enables fast, low-friction transfers, plus strong transparency through public ledgers, making it a robust alternative for people who want more autonomy over how they store and move their value.
When purchasing crypto, make sure you use an exchange that doesn't require Know Your Customer (KYC) checks, which often involves uploading your actual government issued ID, and if the glowies ever track your bitcoin (or shitcoin of choice) transaction history and ask the exchange for your personal information you're fucked.
NOTE: This guide will only cover Monero (XMR) as everything else glows,[it just does, ok??] and is an abridged version of the full guide on the ![]() Darknet Bible.[e]
Darknet Bible.[e]
Monero is private and incredibly difficult to trace, third-parties do not need to be trusted to keep your Monero safe. Not every site accepts this though. Buy Monero on a KYC-free exchange: https://kycnot.me/
Install and create a wallet[edit | edit source]
- Download and install Feather
 [Hidden Service], a lightweight, open-source wallet that works on schizo OS:es like Tails. RTFM. Don't complain if you waste your neetbucks cause (you) couldn't be bothered to read the fucking manual.
[Hidden Service], a lightweight, open-source wallet that works on schizo OS:es like Tails. RTFM. Don't complain if you waste your neetbucks cause (you) couldn't be bothered to read the fucking manual. - Create a wallet in Feather, the new wallet wizard should automatically open when you start Feather.
- On the next page you will be shown the seed allows you to recover your funds in case you lose access to your wallet files. Make sure you keep this seed somewhere safe. Do not save it to your computer or send it anywhere online.[f]
- Click next after you have verified that you have written down all words in the correct order.
- In the Name field, type a name for your wallet. You may name the wallet whatever you want. Feather will automatically fill in a name that hasn’t already been used.
- The Directory field shows the default location for the wallet files. Leave it as default.
- On the next page, choose a password to encrypt your wallet files with. It is recommended to use a strong password generated with a password manager, such as KeePassXC.
- Click on Create/Open wallet to finish wallet creation.
Receiving a Transaction[edit | edit source]
- In feather go to the Receive tab.
- If no addresses show up in the table, click on Create New Address.
- It does not matter which address you choose, funds received to any of the addresses will end up in the same wallet account.
- It is best practice to label an address before you copy it. This way you avoid accidentally reusing the address. Do not hand out addresses to more parties than necessary.
- Copy the address to your clipboard by right-clicking on an address → Copy Address or by pressing Ctrl + C.
- Once an address receives an incoming transaction it is automatically hidden from view. You can unhide used addresses by clicking on Show used.
Sending a Transaction[edit | edit source]
- In feather go to the Send tab
- In the Pay to field, enter the address you want to transfer funds to.
- In the Amount field, enter the amount you want to send. This is the exact amount the recipient will receive, it does not include the miner fee. To send all your balance, click the Max button.
- To construct the transaction, click Send. You will be able to review the transaction details and miner fee before broadcasting.
- After transaction construction is complete, a dialog will pop up asking you to verify the transaction details. To view detailed information, such as the inputs spent in the transaction, click Advanced.
- Click Send to broadcast the transaction after you have verified the details, or Cancel if something is wrong.
Unconfirmed outgoing transactions will show up in the History tab with a gears icon. If several minutes pass and the transaction does not show up in your node’s mempool its status will change to Failed. If the transaction does not show up in a publicly accessible mempool (e.g. xmrchain.net), you may assume the node was unable to relay your transaction.
Uploading images (Removing Metadata)[edit | edit source]
Make sure to always strip the filenames (i.e. replace them with a string of random letters and numbers) and remove the EXIF data of any images you upload.
EXIF data (Exchangeable Image File Format) is a type of metadata used by cameras and smartphones. It can include:
- GPS coordinates of where a photo was taken
- Device make and model
- Shutter speed and aperture
- Time, date, and more
Stripping this information is normally the responsibility of the website before it gets published but some either don't or store it for themselves before stripping it for publishing.
To remove:
- https://exifremover.com/ (if you don't feel like downloading anything)
- https://github.com/szTheory/exifcleaner/releases/tag/v3.6.0 (requires a download but works fast)
Further reading[edit | edit source]
- Darknet Bible:
 http://biblemeowimkh3utujmhm6oh2oeb3ubjw2lpgeq3lahrfr2l6ev6zgyd.onion/
http://biblemeowimkh3utujmhm6oh2oeb3ubjw2lpgeq3lahrfr2l6ev6zgyd.onion/ - Feather Wallet: http://featherwallet.org/
- Feather Wallet hidden service:
 http://featherdvtpi7ckdbkb2yxjfwx3oyvr3xjz3oo4rszylfzjdg6pbm3id.onion/
http://featherdvtpi7ckdbkb2yxjfwx3oyvr3xjz3oo4rszylfzjdg6pbm3id.onion/ - Feather Wallet docs: http://docs.featherwallet.org/ [g]
Notes
- ↑ or a BIOS if your PC is older than dust...
- ↑ Some enthusiast motherboards have a "backup" BIOS you can switch to. That would make this more safe to experiment with.
- ↑ Chromium based browsers include: Chrome[duh], Opera and Opera GX, Brave, Microsoft Edge, and literally every other browser ever that (((they))) control.
- ↑ Previously not recommended as they collaborated with law enforcement to deanonymize specific users, but this turned out to be a huge nothingburger as the person in question had zero OPSEC to begin with, purchased a subscription using their personal credit card and didn't use a VPN.[8]
- ↑ Use Tor to access .onion links
- ↑ On the second page of the create wallet wizard: the wallet seed is shown. You may notice that the seed is shorter than other standard 25 word Monero seed. Feather uses Polyseed for 16 word seeds. To learn more about Polyseed and the benefits compared to 25 word seeds, more info here: https://docs.featherwallet.org/guides/seed-scheme
- ↑ Feather Wallet docs doesnt have a .onion domain
Snopes
- ↑ https://te.mpe.st/blog/20251208-libreboot.html
- ↑ https://gitlab.tails.boum.org/tails/tails/-/issues/5356
- ↑ https://duckduckgo.com/duckduckgo-help-pages/duckai
- ↑ https://github.com/signalapp
- ↑ https://github.com/threema-ch
- ↑ https://threema.com/en/pricing
- ↑ https://threema.com/en/faq/privacy-protection
- ↑ Original article (Paywalled) Archive without paywall
- ↑ https://wiki.archlinux.org/title/Tor#Proxy_Configuration
➜ /languages
➜ /software
├ /imageboards/ nusoi • Vichan • Yotsuba • OpenYotsuba
├ /operating_systems/ Windows • Linux • Android • TempleOS • BSD
├ /applications/ Web Browser • Photoshop • Flash • MS Paint • IRC
├ /dev/ Free-software license • Game development
└ /misc/ Babybot • McChallenge • CAPTCHA • Systemd • RAID • Ricing • 4get • Snarkysnappydoxingtool.bat • JS Paint • Soyjak Party Enhanced
➜ /cyb
➜ /ai
└ ChatGPT • Gemini • Grok • Vibe coding • Generative AI • Stable Diffusion

